- Print
- PDF
Applies to: Lasernet Core 11
Security roles are used for specifying user permissions for Lasernet Developer and Manage.
Go to Manage and manage your Lasernet Core users, groups and security roles. For more information about this configuration area, see Configure Users, Groups, and Security Roles.
Security role members can be users or groups. On the Security Roles page of Manage, the Job Status roles control rights for document management on the Job Status page of Manage.
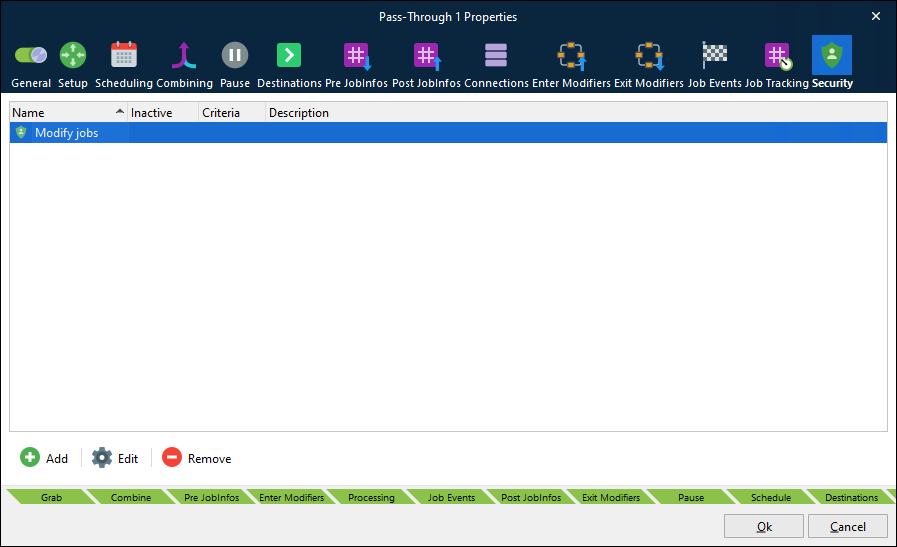
The Job Status security roles can be added to any module available in the configuration (on the module’s Security tab). When a job is saved, Lasernet Core will refer to the security roles listed there; if the module has no security role listed, the job is visible to job administrators only. Roles determine who is allowed to view and manage specific paused, scheduled or failed jobs on the Job Status page. You can add criteria to each assignment on the Security tab.
In addition to adding security roles to the Security tab, you can also add security profiles. For more information, see Security Profiles.
Security Profiles
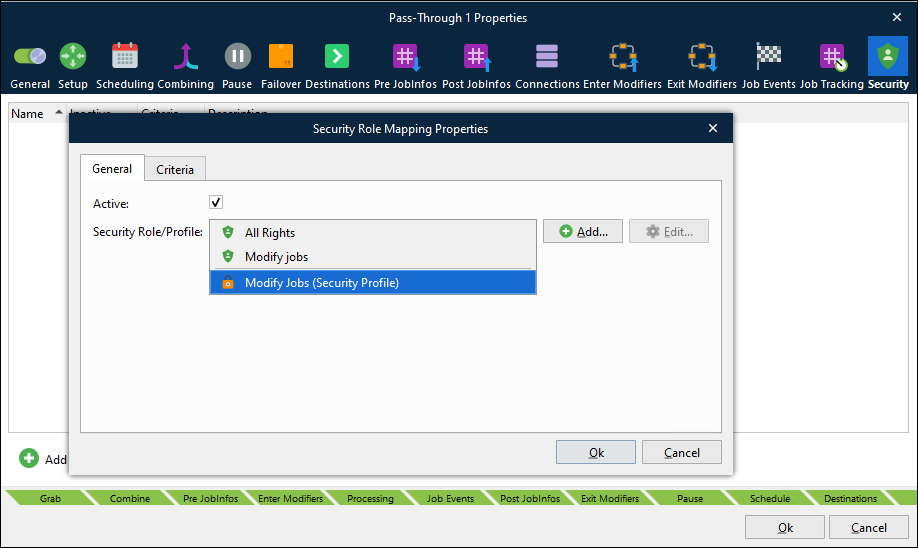
Security Profiles enable you to assign multiple security roles to a module as a single security profile.
When you create a security profile, you can add multiple security roles to it. Also, you can add criteria to each of these security role assignments.
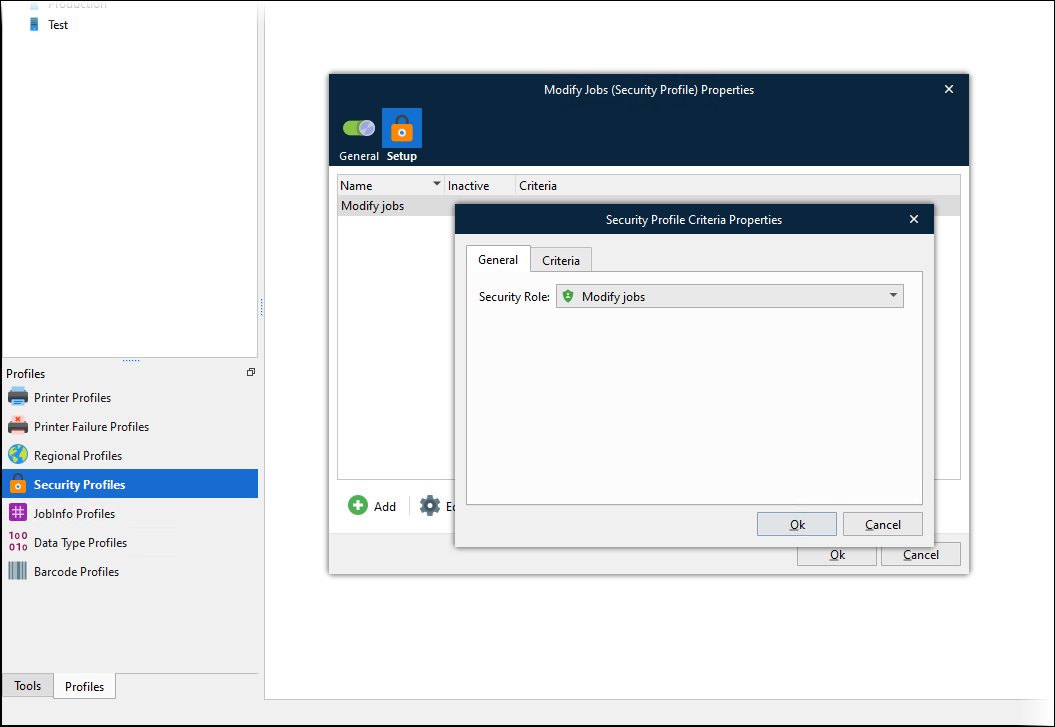
After you create a security profile, you can add it to a module’s Security tab (along with individual security roles).
Users, Groups, and Permissions
For comprehensive information about Lasernet Core permissions and user, group, and security role configuration, see Configure Users, Groups, and Security Roles.